CPCSC Is Required Starting Summer 2026.
85% of organizations fail their first NIST 800-171 assessment.
Is your company ready?
Get an assessment →Call Plurilock™ First.
Trusted help for CISOs and CIOs facing their toughest challenges—or cyber risks that have suddenly become cyber realities.
Talk to an expert →One Call. Every Solution.
Professional services, managed IT, and hundreds of thousands of software and hardware products—all from one trusted partner.
We can help →Services led.
Product enabled.
AI native.
Meet today’s Plurilock: Solving the free world’s toughest cyber problems for the free world’s most important enterprises.
Learn more →Introducing Code and Country (a podcast)
Leading voices from government and industry discuss the ways in which today, cybersecurity is national security.
 Listen now →
Listen now →{ Sovereign, AI-Native Cyber Resilience }
Sovereign Canadian • Built for critical needs • Platform backed • Not partner dependent • Innovation deployed • R&D securing reality
Plurilock brings research-driven quantum, AI, agentive security, and resilience engineering to enterprises that operate at the edge of tomorrow.
Feel like you're paying for cyber overhead, not cyber execution?
- Elite
practitionersnot process
managers - We solve
problemsnot just
meet about them - Delivered
outcomesnot just
deliverables - We find the vulnerabilities others miss, integrate the systems others struggle with, and deliver the outcomes others delay.
Get better execution →
Need a provider that moves at the speed of the threat?
- When other providers tell you it'll be weeks or even months to spin up, contact us—we can often mobilize in just days.
Get started rapidly → - Spin-up
in daysno preliminaries
for months - Forward
movementnot just
meetings - Your
timelineis ours and
informs our work
Stacking solutions but not effectiveness?
- Fewer
toolsmore
security - Real
integration
that
actually works - We work
for younot for
vendors - We won't sell you solutions you don't need—we find ways to make environments simple, lean, and maximally effective.
Consolidate and level up →
Need sovereign, AI-native resilience in Canada?
- From agentic cyber to post-quantum readiness, we're building the sovereign capabilities that Canada and the world need.
Discover our platform → - Canadian
IPbuilt for
critical needs - Platform-
backednot partner-
dependent - Innovation
deployedR&D that becomes
reality
Let’s get started.
Built on proprietary research and sovereign Canadian innovation, we solve today's threats while building tomorrow's resilience.
Most of our engagements begin with one of these steps.
Learn more about our services.
AI-native and built on sovereign Canadian innovation, Plurilock solves today's threats while building tomorrow's resilience.

Beyond Governance, Risk, and Compliance
Compliance • Third-Party Risk • Vulnerability Mgmt. • Audit Rediness • Asset Mgmt.
Learn more →
Cloud Security Services
CASB • Cloud Visibility • Cloud Guardrails • Multi-Cloud Hardening • Cloud Governance
Learn more →
Data Protection Services
Zero Trust • Data Loss Prevention (DLP) • Identity and Access Mgmt. (IAM) • PKI and Encryption
Learn more →
Cyber Adversary Simulation and Response Services
Pen Test • Red Team • Tabletop • Ransomware and Social Engineering • App, API, AI, SCADA
Learn more →
Or just ask.
Whatever your situation, we’re here to help.
Let’s schedule a time to talk.
loading...
Plurilock™ is publicly traded as TSXV:PLUR and QTCQB:PLCKF Learn more →
Code and Country: Matt O'Neill
Matt is a retired Secret Service senior executive who spent 25 years leading cyber crime investigations.
Watch the episode →Code and Country: Carey Frey
Carey Frey brings a rare dual perspective on security from both sides of the public-private divide
Watch the episode →Meet Plurilock's Team
Hear from the senior leaders responsible for Plurilock, its rapid growth, and its industry-leading capabilities.
Listen now →Securing Operational Technology
Actionable, practical tips on securing today's industrial control and operational technology systems.
Watch the webinar →Erecting Guardrails for AI
Find out what you need to do to ensure that AI serves your organization safely, rather than breaking things, in this white paper.
 Read the PDF →
Read the PDF →Cybersecurity Reference
Get help with common cybersecurity terms, concepts, solutions and needs—plus statistics, specialty topic deep-dives, and more.
Dive in →Practical Cyber Cheat Sheet
Just the facts—the simple steps to stay secure, plus the steps you should take if things go wrong.
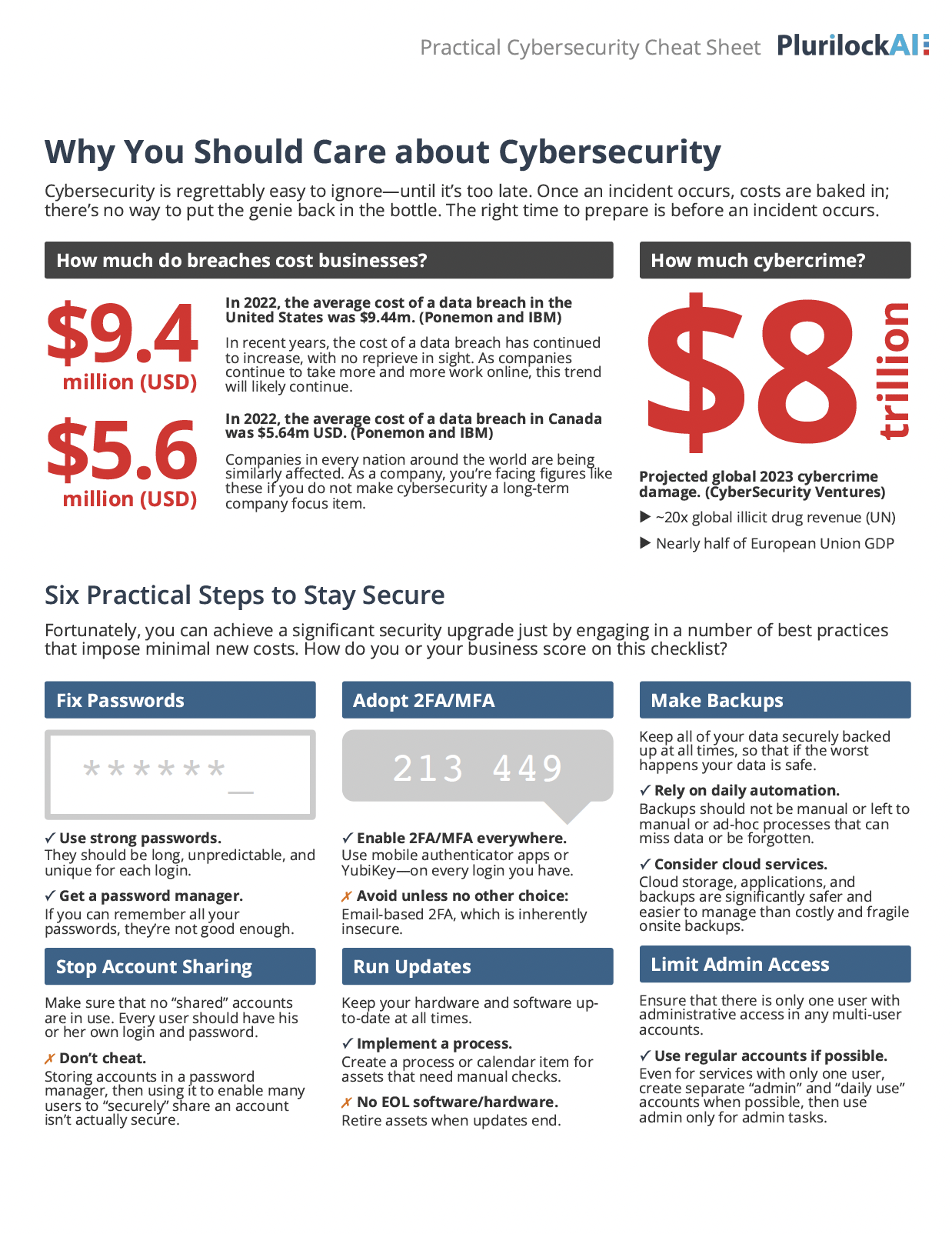 Read the PDF →
Read the PDF →Latest Press
Latest Resource
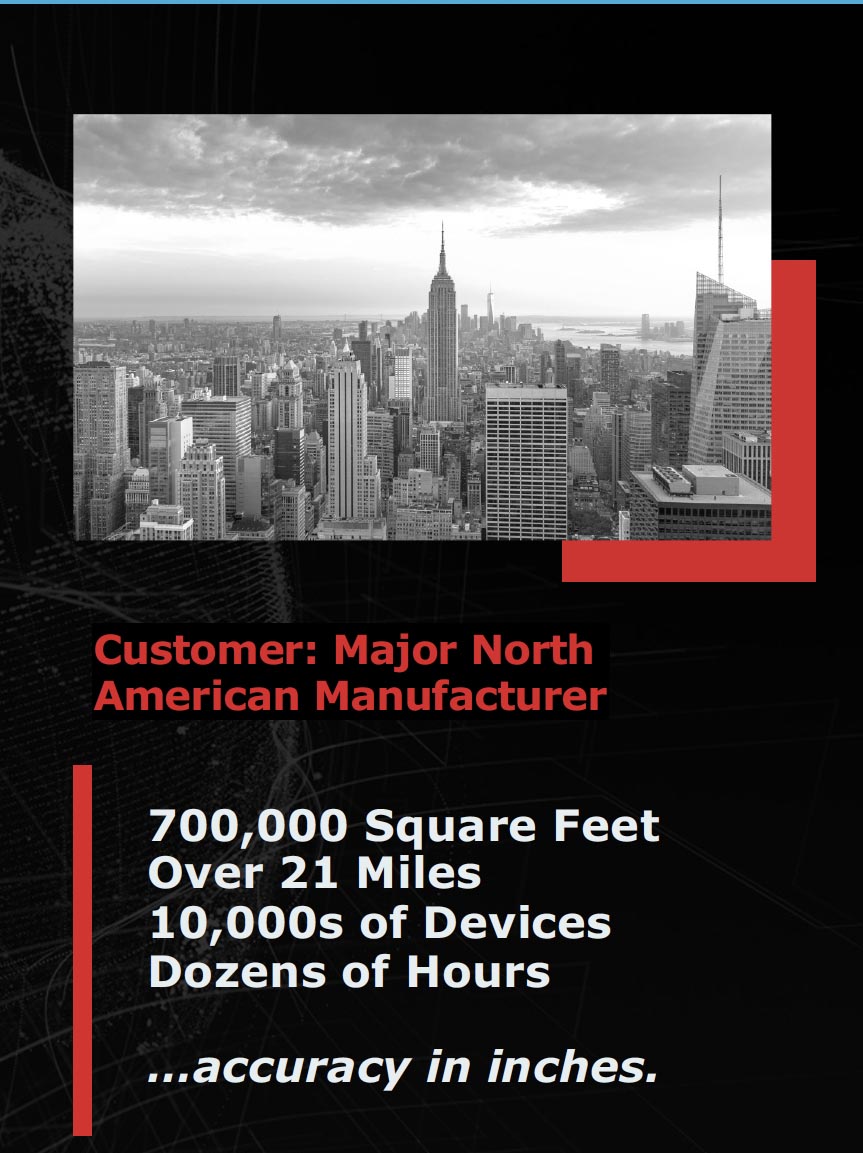
You know you’ve solved your client’s problem when the Director of SecDevOps calls your engagement an “overwhelming success” and your team “indispensable.”